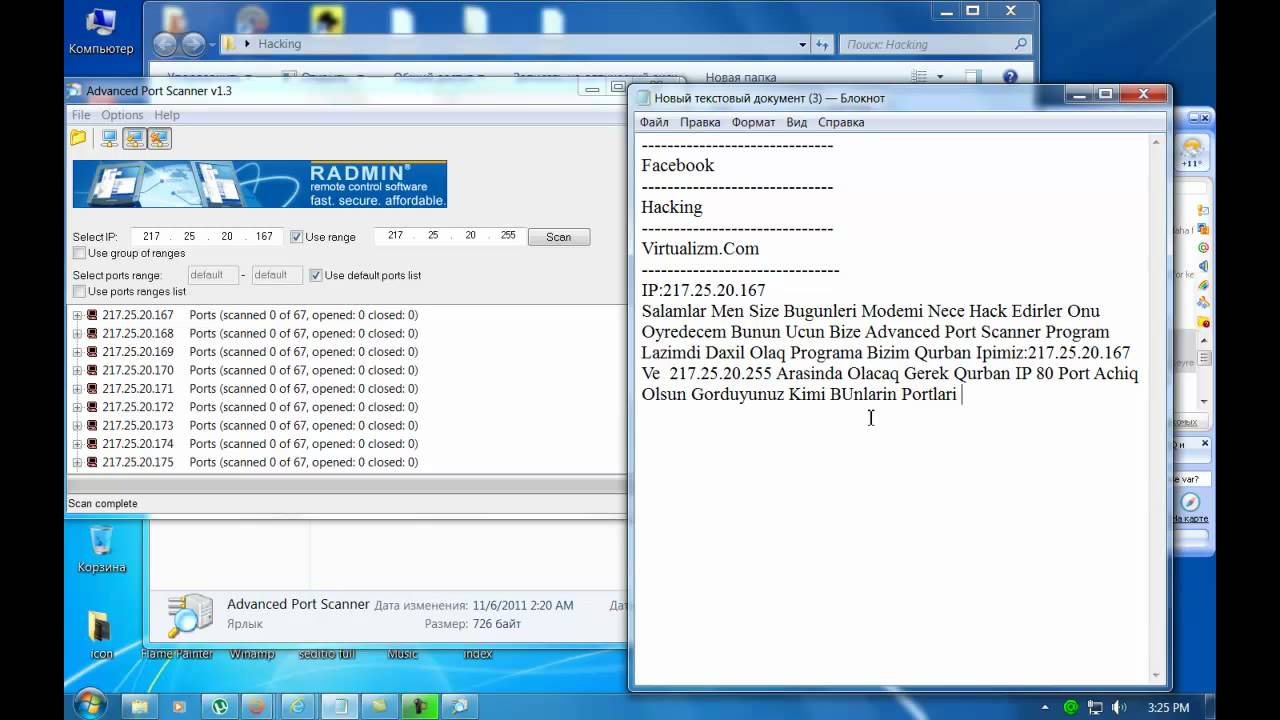
Hacking With Advanced Port Scanner Software

OK About this tool allows you to discover which TCP ports are open on your target host. Network ports are the entry points to a machine that is connected to the Internet. A service that listens on a port is able to receive data from a client application, process it and send a response back. Fight Night Champion Keygen Safe. Anatomia Humana Latarjet Tomo 2 Pdf more. Malicious clients can sometimes exploit vulnerabilities in the server code so they gain access to sensitive data or execute malicious code on the machine remotely. That is why testing for all ports is necessary in order to achieve a thorough security verification.
Port scanning is usually done in the initial phase of a penetration test in order to discover all network entry points into the target system. Port scanning is done differently for TCP ports and for UDP ports that's why we have different tools.
Parameters • Target: This is the hostname of IP address(es) to scan • Ports to scan - Common: This option tells Nmap to scan only the top 100 most common TCP ports (Nmap -F). • Ports to scan - Range: You can specify a range of ports to be scanned.
(like ethereal hacking) & best to download hacking tools. Powerful TCP port scanner. I just search from Google about hacking software and i found top-15.
May 1, 2010 - This is how to hack a computer for educational purposes. First you need its IP address, radmin viewer 3.3 or later, and an open port scanner. Okay so first you need the IP and scan the IP address of the computer. Now find what open port it has. Ok then open up radmin viewer and put in the IP address and. Apr 17, 2006 - SuperScan 4 is an update of the highly popular Windows port scanning tool, SuperScan. Also see – Superscan v4.0 – Fast TCP & UDP Port Scanner for Windows. To finish off your download hacking tools mission, something a little more advanced if you want to test your TCP/IP packet monkey skills.
Valid ports are between 1 and 65535. • Ports to scan - List: You can specify a comma separated list of ports to be scanned. • Detect service version: In this case Nmap will try to detect the version of the service that is running on each open port. This is done using multiple techniques like banner grabbing, reading server headers and sending specific requests.